Apr 25, 2017 For more details on the configuration process, check out Remote Desktop Gateway and Azure Muti-Factor Authentication Server using RADIUS. By the way, here is a blog about use windows server 2012 R2 RD Gateway with MFA. Following the instructions i was able to enable MFA for some users, but it only works for Office 365 online login, and with Microsoft desktop apps (eg. Outlook 2016) with app password. Is it even possible to setup Microsoft Authenticator for console and RDP login, with or without on-premise MFA Server? The Microsoft Authenticator app also supports the industry standard for time-based, one-time passcodes (also known as TOTP or OTP). Because of that, you can add any online account that also supports this standard to the Microsoft Authenticator app. This will help keep your other online accounts secure.
- Microsoft Authenticator Remote Desktop Login
- Microsoft Authenticator Remote Desktop Download
- Microsoft Authenticator Remote Desktop App
This article provides details for integrating your Remote Desktop Gateway infrastructure with Azure AD Multi-Factor Authentication (MFA) using the Network Policy Server (NPS) extension for Microsoft Azure.
The Network Policy Server (NPS) extension for Azure allows customers to safeguard Remote Authentication Dial-In User Service (RADIUS) client authentication using Azure's cloud-based Multi-Factor Authentication (MFA). This solution provides two-step verification for adding a second layer of security to user sign-ins and transactions.
This article provides step-by-step instructions for integrating the NPS infrastructure with Azure AD MFA using the NPS extension for Azure. This enables secure verification for users attempting to sign in to a Remote Desktop Gateway.
Note
This article should not be used with MFA Server deployments and should only be used with Azure AD MFA (Cloud-based) deployments.
The Network Policy and Access Services (NPS) gives organizations the ability to do the following:
- Define central locations for the management and control of network requests by specifying who can connect, what times of day connections are allowed, the duration of connections, and the level of security that clients must use to connect, and so on. Rather than specifying these policies on each VPN or Remote Desktop (RD) Gateway server, these policies can be specified once in a central location. The RADIUS protocol provides the centralized Authentication, Authorization, and Accounting (AAA).
- Establish and enforce Network Access Protection (NAP) client health policies that determine whether devices are granted unrestricted or restricted access to network resources.
- Provide a means to enforce authentication and authorization for access to 802.1x-capable wireless access points and Ethernet switches.
Typically, organizations use NPS (RADIUS) to simplify and centralize the management of VPN policies. However, many organizations also use NPS to simplify and centralize the management of RD Desktop Connection Authorization Policies (RD CAPs).
Organizations can also integrate NPS with Azure AD MFA to enhance security and provide a high level of compliance. This helps ensure that users establish two-step verification to sign in to the Remote Desktop Gateway. For users to be granted access, they must provide their username/password combination along with information that the user has in their control. This information must be trusted and not easily duplicated, such as a cell phone number, landline number, application on a mobile device, and so on. RDG currently supports phone call and push notifications from Microsoft authenticator app methods for 2FA. For more information about supported authentication methods see the section Determine which authentication methods your users can use.
Prior to the availability of the NPS extension for Azure, customers who wished to implement two-step verification for integrated NPS and Azure AD MFA environments had to configure and maintain a separate MFA Server in the on-premises environment as documented in Remote Desktop Gateway and Azure Multi-Factor Authentication Server using RADIUS.
The availability of the NPS extension for Azure now gives organizations the choice to deploy either an on-premises based MFA solution or a cloud-based MFA solution to secure RADIUS client authentication.
Authentication Flow
For users to be granted access to network resources through a Remote Desktop Gateway, they must meet the conditions specified in one RD Connection Authorization Policy (RD CAP) and one RD Resource Authorization Policy (RD RAP). RD CAPs specify who is authorized to connect to RD Gateways. RD RAPs specify the network resources, such as remote desktops or remote apps, that the user is allowed to connect to through the RD Gateway.
An RD Gateway can be configured to use a central policy store for RD CAPs. RD RAPs cannot use a central policy, as they are processed on the RD Gateway. An example of an RD Gateway configured to use a central policy store for RD CAPs is a RADIUS client to another NPS server that serves as the central policy store.
When the NPS extension for Azure is integrated with the NPS and Remote Desktop Gateway, the successful authentication flow is as follows:
- The Remote Desktop Gateway server receives an authentication request from a remote desktop user to connect to a resource, such as a Remote Desktop session. Acting as a RADIUS client, the Remote Desktop Gateway server converts the request to a RADIUS Access-Request message and sends the message to the RADIUS (NPS) server where the NPS extension is installed.
- The username and password combination is verified in Active Directory and the user is authenticated.
- If all the conditions as specified in the NPS Connection Request and the Network Policies are met (for example, time of day or group membership restrictions), the NPS extension triggers a request for secondary authentication with Azure AD MFA.
- Azure AD MFA communicates with Azure AD, retrieves the user's details, and performs the secondary authentication using supported methods.
- Upon success of the MFA challenge, Azure AD MFA communicates the result to the NPS extension.
- The NPS server, where the extension is installed, sends a RADIUS Access-Accept message for the RD CAP policy to the Remote Desktop Gateway server.
- The user is granted access to the requested network resource through the RD Gateway.
Prerequisites
Microsoft Authenticator Remote Desktop Login
This section details the prerequisites necessary before integrating Azure AD MFA with the Remote Desktop Gateway. Before you begin, you must have the following prerequisites in place.
- Remote Desktop Services (RDS) infrastructure
- Azure AD MFA License
- Windows Server software
- Network Policy and Access Services (NPS) role
- Azure Active Directory synched with on-premises Active Directory
- Azure Active Directory GUID ID
Remote Desktop Services (RDS) infrastructure

You must have a working Remote Desktop Services (RDS) infrastructure in place. If you do not, then you can quickly create this infrastructure in Azure using the following quickstart template: Create Remote Desktop Session Collection deployment.
If you wish to manually create an on-premises RDS infrastructure quickly for testing purposes, follow the steps to deploy one.Learn more: Deploy RDS with Azure quickstart and Basic RDS infrastructure deployment.
Azure AD MFA License
Required is a license for Azure AD MFA, which is available through Azure AD Premium or other bundles that include it. Consumption-based licenses for Azure AD MFA, such as per user or per authentication licenses, are not compatible with the NPS extension. For more information, see How to get Azure AD Multi-Factor Authentication. For testing purposes, you can use a trial subscription.
Windows Server software
The NPS extension requires Windows Server 2008 R2 SP1 or above with the NPS role service installed. All the steps in this section were performed using Windows Server 2016.
Network Policy and Access Services (NPS) role
The NPS role service provides the RADIUS server and client functionality as well as Network Access Policy health service. This role must be installed on at least two computers in your infrastructure: The Remote Desktop Gateway and another member server or domain controller. By default, the role is already present on the computer configured as the Remote Desktop Gateway. You must also install the NPS role on at least on another computer, such as a domain controller or member server.
For information on installing the NPS role service Windows Server 2012 or older, see Install a NAP Health Policy Server. For a description of best practices for NPS, including the recommendation to install NPS on a domain controller, see Best Practices for NPS.
Azure Active Directory synched with on-premises Active Directory
To use the NPS extension, on-premises users must be synced with Azure AD and enabled for MFA. This section assumes that on-premises users are synched with Azure AD using AD Connect. For information on Azure AD connect, see Integrate your on-premises directories with Azure Active Directory.
Azure Active Directory GUID ID
To install NPS extension, you need to know the GUID of the Azure AD. Instructions for finding the GUID of the Azure AD are provided below.
Configure Multi-Factor Authentication
This section provides instructions for integrating Azure AD MFA with the Remote Desktop Gateway. As an administrator, you must configure the Azure AD MFA service before users can self-register their multi-factor devices or applications.
Follow the steps in Getting started with Azure AD Multi-Factor Authentication in the cloud to enable MFA for your Azure AD users.
Configure accounts for two-step verification
Once an account has been enabled for MFA, you cannot sign in to resources governed by the MFA policy until you have successfully configured a trusted device to use for the second authentication factor and have authenticated using two-step verification.
Follow the steps in What does Azure AD Multi-Factor Authentication mean for me? to understand and properly configure your devices for MFA with your user account.
Important
The sign-in behavior for Remote Desktop Gateway doesn't provide the option to enter a verification code with Azure AD Multi-Factor Authentication. A user account must be configured for phone verification or the Microsoft Authenticator App with push notifications.
If neither phone verification or the Microsoft Authenticator App with push notifications is configured for a user, the user won't be able to complete the Azure AD Multi-Factor Authentication challenge and sign in to Remote Desktop Gateway.
The SMS text method doesn't work with Remote Desktop Gateway because it doesn't provide the option to enter a verification code.
Install and configure NPS extension
This section provides instructions for configuring RDS infrastructure to use Azure AD MFA for client authentication with the Remote Desktop Gateway.
Acquire Azure Active Directory tenant ID
As part of the configuration of the NPS extension, you need to supply admin credentials and the Azure AD ID for your Azure AD tenant. To get the tenant ID, complete the following steps:
Sign in to the Azure portal as the global administrator of the Azure tenant.
In the Azure portal menu, select Azure Active Directory, or search for and select Azure Active Directory from any page.
On the Overview page, the Tenant information is shown. Next to the Tenant ID, select the Copy icon, as shown in the following example screenshot:
Install the NPS extension
Install the NPS extension on a server that has the Network Policy and Access Services (NPS) role installed. This functions as the RADIUS server for your design.
Important
Don't install the NPS extension on your Remote Desktop Gateway (RDG) server. The RDG server doesn't use the RADIUS protocol with its client, so the extension can't interpret and perform the MFA.
When the RDG server and NPS server with NPS extension are different servers, RDG uses NPS internally to talk to other NPS servers and uses RADIUS as the protocol to correctly communicate.
- Download the NPS extension.
- Copy the setup executable file (NpsExtnForAzureMfaInstaller.exe) to the NPS server.
- On the NPS server, double-click NpsExtnForAzureMfaInstaller.exe. If prompted, click Run.
- In the NPS Extension For Azure AD MFA Setup dialog box, review the software license terms, check I agree to the license terms and conditions, and click Install.
- In the NPS Extension For Azure AD MFA Setup dialog box, click Close.
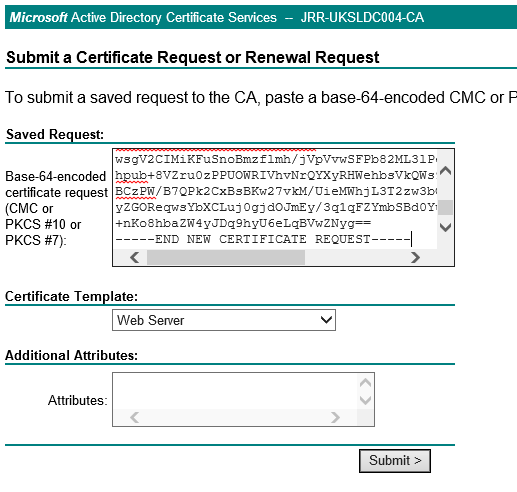
Configure certificates for use with the NPS extension using a PowerShell script
Next, you need to configure certificates for use by the NPS extension to ensure secure communications and assurance. The NPS components include a Windows PowerShell script that configures a self-signed certificate for use with NPS.
The script performs the following actions:
- Creates a self-signed certificate
- Associates public key of certificate to service principal on Azure AD
- Stores the cert in the local machine store
- Grants access to the certificate's private key to the network user
- Restarts Network Policy Server service
If you want to use your own certificates, you need to associate the public key of your certificate to the service principal on Azure AD, and so on.
To use the script, provide the extension with your Azure AD Admin credentials and the Azure AD tenant ID that you copied earlier. Run the script on each NPS server where you installed the NPS extension. Then do the following:
Open an administrative Windows PowerShell prompt.
At the PowerShell prompt, type
cd 'c:Program FilesMicrosoftAzureMfaConfig', and press ENTER.Type
.AzureMfaNpsExtnConfigSetup.ps1, and press ENTER. The script checks to see if the Azure Active Directory PowerShell module is installed. If not installed, the script installs the module for you.After the script verifies the installation of the PowerShell module, it displays the Azure Active Directory PowerShell module dialog box. In the dialog box, enter your Azure AD admin credentials and password, and click Sign In.
When prompted, paste the Tenant ID you copied to the clipboard earlier, and press ENTER.
The script creates a self-signed certificate and performs other configuration changes. The output should be like the image shown below.
Configure NPS components on Remote Desktop Gateway
In this section, you configure the Remote Desktop Gateway connection authorization policies and other RADIUS settings.
The authentication flow requires that RADIUS messages be exchanged between the Remote Desktop Gateway and the NPS server where the NPS extension is installed. This means that you must configure RADIUS client settings on both Remote Desktop Gateway and the NPS server where the NPS extension is installed.
Configure Remote Desktop Gateway connection authorization policies to use central store
Remote Desktop connection authorization policies (RD CAPs) specify the requirements for connecting to a Remote Desktop Gateway server. RD CAPs can be stored locally (default) or they can be stored in a central RD CAP store that is running NPS. To configure integration of Azure AD MFA with RDS, you need to specify the use of a central store.
On the RD Gateway server, open Server Manager.
On the menu, click Tools, point to Remote Desktop Services, and then click Remote Desktop Gateway Manager.
In the RD Gateway Manager, right-click [Server Name] (Local), and click Properties.
In the Properties dialog box, select the RD CAP Store tab.
On the RD CAP Store tab, select Central server running NPS.
In the Enter a name or IP address for the server running NPS field, type the IP address or server name of the server where you installed the NPS extension.
Click Add.
In the Shared Secret dialog box, enter a shared secret, and then click OK. Ensure you record this shared secret and store the record securely.
Note
Shared secret is used to establish trust between the RADIUS servers and clients. Create a long and complex secret.
Click OK to close the dialog box.
Configure RADIUS timeout value on Remote Desktop Gateway NPS
To ensure there is time to validate users' credentials, perform two-step verification, receive responses, and respond to RADIUS messages, it is necessary to adjust the RADIUS timeout value.
On the RD Gateway server, open Server Manager. On the menu, click Tools, and then click Network Policy Server.
In the NPS (Local) console, expand RADIUS Clients and Servers, and select Remote RADIUS Server.
In the details pane, double-click TS GATEWAY SERVER GROUP.
Note
This RADIUS Server Group was created when you configured the central server for NPS policies. The RD Gateway forwards RADIUS messages to this server or group of servers, if more than one in the group.
In the TS GATEWAY SERVER GROUP Properties dialog box, select the IP address or name of the NPS server you configured to store RD CAPs, and then click Edit.
In the Edit RADIUS Server dialog box, select the Load Balancing tab.
In the Load Balancing tab, in the Number of seconds without response before request is considered dropped field, change the default value from 3 to a value between 30 and 60 seconds.
In the Number of seconds between requests when server is identified as unavailable field, change the default value of 30 seconds to a value that is equal to or greater than the value you specified in the previous step.
Click OK two times to close the dialog boxes.
Verify Connection Request Policies
By default, when you configure the RD Gateway to use a central policy store for connection authorization policies, the RD Gateway is configured to forward CAP requests to the NPS server. The NPS server with the Azure AD MFA extension installed, processes the RADIUS access request. The following steps show you how to verify the default connection request policy.
On the RD Gateway, in the NPS (Local) console, expand Policies, and select Connection Request Policies.
Double-click TS GATEWAY AUTHORIZATION POLICY.
In the TS GATEWAY AUTHORIZATION POLICY properties dialog box, click the Settings tab.
On Settings tab, under Forwarding Connection Request, click Authentication. RADIUS client is configured to forward requests for authentication.
Click Cancel.
Note
For more information about creating a connection request policy see the article, Configure connection request policies documentation for the same.
Configure NPS on the server where the NPS extension is installed
The NPS server where the NPS extension is installed needs to be able to exchange RADIUS messages with the NPS server on the Remote Desktop Gateway. To enable this message exchange, you need to configure the NPS components on the server where the NPS extension service is installed.
Register Server in Active Directory
To function properly in this scenario, the NPS server needs to be registered in Active Directory.
On the NPS server, open Server Manager.
In Server Manager, click Tools, and then click Network Policy Server.
In the Network Policy Server console, right-click NPS (Local), and then click Register server in Active Directory.
Click OK two times.
Leave the console open for the next procedure.
Create and configure RADIUS client
The Remote Desktop Gateway needs to be configured as a RADIUS client to the NPS server.
On the NPS server where the NPS extension is installed, in the NPS (Local) console, right-click RADIUS Clients and click New.
In the New RADIUS Client dialog box, provide a friendly name, such as Gateway, and the IP address or DNS name of the Remote Desktop Gateway server.
In the Shared secret and the Confirm shared secret fields, enter the same secret that you used before.
Click OK to close the New RADIUS Client dialog box.
Configure Network Policy
Recall that the NPS server with the Azure AD MFA extension is the designated central policy store for the Connection Authorization Policy (CAP). Therefore, you need to implement a CAP on the NPS server to authorize valid connections requests.
Microsoft Authenticator Remote Desktop Download
On the NPS Server, open the NPS (Local) console, expand Policies, and click Network Policies.
Right-click Connections to other access servers, and click Duplicate Policy.
Right-click Copy of Connections to other access servers, and click Properties.
In the Copy of Connections to other access servers dialog box, in Policy name, enter a suitable name, such as RDG_CAP. Check Policy enabled, and select Grant access. Optionally, in Type of network access server, select Remote Desktop Gateway, or you can leave it as Unspecified.
Click the Constraints tab, and check Allow clients to connect without negotiating an authentication method.
Optionally, click the Conditions tab and add conditions that must be met for the connection to be authorized, for example, membership in a specific Windows group.
Click OK. When prompted to view the corresponding Help topic, click No.
Ensure that your new policy is at the top of the list, that the policy is enabled, and that it grants access.
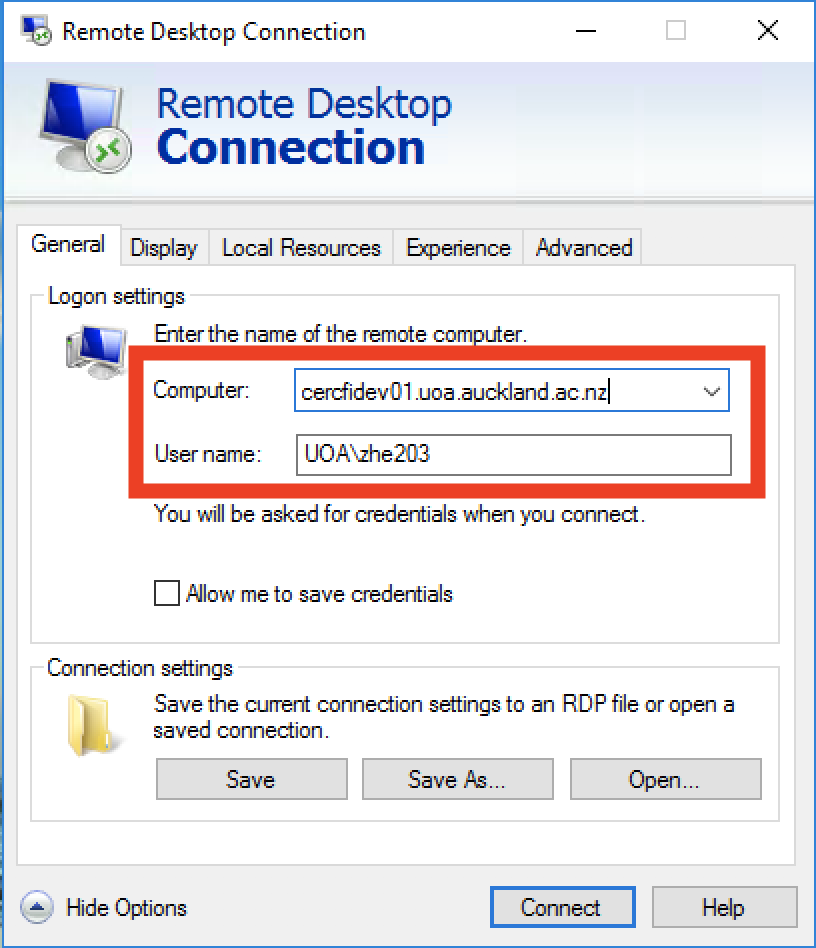
Verify configuration
To verify the configuration, you need to sign in to the Remote Desktop Gateway with a suitable RDP client. Be sure to use an account that is allowed by your Connection Authorization Policies and is enabled for Azure AD MFA.
As show in the image below, you can use the Remote Desktop Web Access page.
Upon successfully entering your credentials for primary authentication, the Remote Desktop Connect dialog box shows a status of Initiating remote connection, as shown below.
If you successfully authenticate with the secondary authentication method you previously configured in Azure AD MFA, you are connected to the resource. However, if the secondary authentication is not successful, you are denied access to the resource.
In the example below, the Authenticator app on a Windows phone is used to provide the secondary authentication.
Once you have successfully authenticated using the secondary authentication method, you are logged into the Remote Desktop Gateway as normal. However, because you are required to use a secondary authentication method using a mobile app on a trusted device, the sign in process is more secure than it would be otherwise.
View Event Viewer logs for successful logon events
To view the successful sign-in events in the Windows Event Viewer logs, you can issue the following Windows PowerShell command to query the Windows Terminal Services and Windows Security logs.
To query successful sign-in events in the Gateway operational logs (Event ViewerApplications and Services LogsMicrosoftWindowsTerminalServices-GatewayOperational), use the following PowerShell commands:
Get-WinEvent -Logname Microsoft-Windows-TerminalServices-Gateway/Operational | where {$_.ID -eq '300'} | FL- This command displays Windows events that show the user met resource authorization policy requirements (RD RAP) and was granted access.
Get-WinEvent -Logname Microsoft-Windows-TerminalServices-Gateway/Operational | where {$_.ID -eq '200'} | FL- This command displays the events that show when user met connection authorization policy requirements.
You can also view this log and filter on event IDs, 300 and 200. To query successful logon events in the Security event viewer logs, use the following command:
Get-WinEvent -Logname Security | where {$_.ID -eq '6272'} | FL- This command can be run on either the central NPS or the RD Gateway Server.
You can also view the Security log or the Network Policy and Access Services custom view, as shown below:
On the server where you installed the NPS extension for Azure AD MFA, you can find Event Viewer application logs specific to the extension at Application and Services LogsMicrosoftAzureMfa.
Troubleshoot Guide
If the configuration is not working as expected, the first place to start to troubleshoot is to verify that the user is configured to use Azure AD MFA. Have the user connect to the Azure portal. If users are prompted for secondary verification and can successfully authenticate, you can eliminate an incorrect configuration of Azure AD MFA.
If Azure AD MFA is working for the user(s), you should review the relevant Event logs. These include the Security Event, Gateway operational, and Azure AD MFA logs that are discussed in the previous section.
Below is an example output of Security log showing a failed logon event (Event ID 6273).
Below is a related event from the AzureMFA logs:
To perform advanced troubleshoot options, consult the NPS database format log files where the NPS service is installed. These log files are created in %SystemRoot%System32Logs folder as comma-delimited text files.
For a description of these log files, see Interpret NPS Database Format Log Files. The entries in these log files can be difficult to interpret without importing them into a spreadsheet or a database. You can find several IAS parsers online to assist you in interpreting the log files.
The image below shows the output of one such downloadable shareware application.
Finally, for additional troubleshoot options, you can use a protocol analyzer, such Microsoft Message Analyzer.
The image below from Microsoft Message Analyzer shows network traffic filtered on RADIUS protocol that contains the user name CONTOSOAliceC.
Next steps
Description
This feature is only available for the following data sources: Devolutions Server, MariaDB, Microsoft Access, Microsoft SQL Azure, Microsoft SQL Server, MySQL and SQLite. |
Two-factor authentication identifies users by two different components: something that the user knows (often a password) and something that the user possesses (e.g. a validation code sent to a mobile device).
If one of the components is missing or supplied incorrectly, the user's identity is not established with sufficient certainty and then access to the data source will remain blocked.
Microsoft Authenticator Remote Desktop App
Remote Desktop Manager supports Google Authenticator, Yubikey, Duo and AuthAnvil.
How to Configure Two-Factor Authentication
Example of how to configure 2FA with Google Authenticator
Settings
1. Two factor authentication is set in the Data Source Configuration. You can set 2FA when creating a new data source or edit an existing data source. To edit your data source, click File – Data Sources. Click the pencil to edit the data source.
2. To set 2FA on the data source, click the None hyperlink.
3. In the next window, click Change.
3. Choose the type of 2-Factor Authentication you wish to use.
4. Once you have selected your 2FA click Save to start the configuration.
To configure the 2FA you use, please see the topic about supported 2FA types:
•Google Authenticator
•Yubikey
•Duo
•AuthAnvil
